Since the beginning of 2023, 78 attributed threat actors have targeted public safety across 171 attacks, with an additional 44 attacks conducted by unknown adversaries. A new report from the Public Safety Threat Alliance (PSTA) focuses on the emerging cyber threat actors targeting public safety this year in these attacks. It reveals their tactics and motivations, as well as those of returning adversaries. Here are some highlights from the report, which is available now to PSTA members.
In addition to the usual suspects, there’s been a significant uptick in emerging threat actors this year, with 26 percent of public safety cyber attacks initiated by new groups or groups that haven’t targeted public safety agencies before. The tactics and motivations of these novel groups differ from those of established threat actors.
While ransomware, or extortion, remains the most common cyber threat against public safety overall, these new groups are more likely to be initial access brokers (IABs).
New in Town: IABs
Many novel threat actors are IABs motivated by financial gain who take advantage of the relatively lower technical and operational requirements for such attacks. Once these cybercriminals get access to a victim’s network, they sell that access to other threat actors targeting sensitive data, acting as brokers in the process.
While IAB activity tends to be a starting point for emerging threat actors targeting public safety, it is often a precursor to more lucrative extortion attacks as they mature in capability and experience. New threat actors were only responsible for 19 percent of extortion attacks at the beginning of 2023, but that number has grown to 37 percent in the last few months.
Notable Threat Groups
While many new threat actors were identified in 2023, the most notable ones targeting public safety were the Royal extortion syndicate, the cybercriminal group TwoFactor and the hacktivist collective Anonymous Sudan.
These groups are known to claim their attacks via criminal forums, marketplaces, messaging platforms and sites such as XSS, where they can advertise access to the victims whose systems they’ve hacked. This differs from extortion groups, which commonly claim responsibility for attacks via dedicated leak sites where they publish stolen information.
Keeping Systems Safe
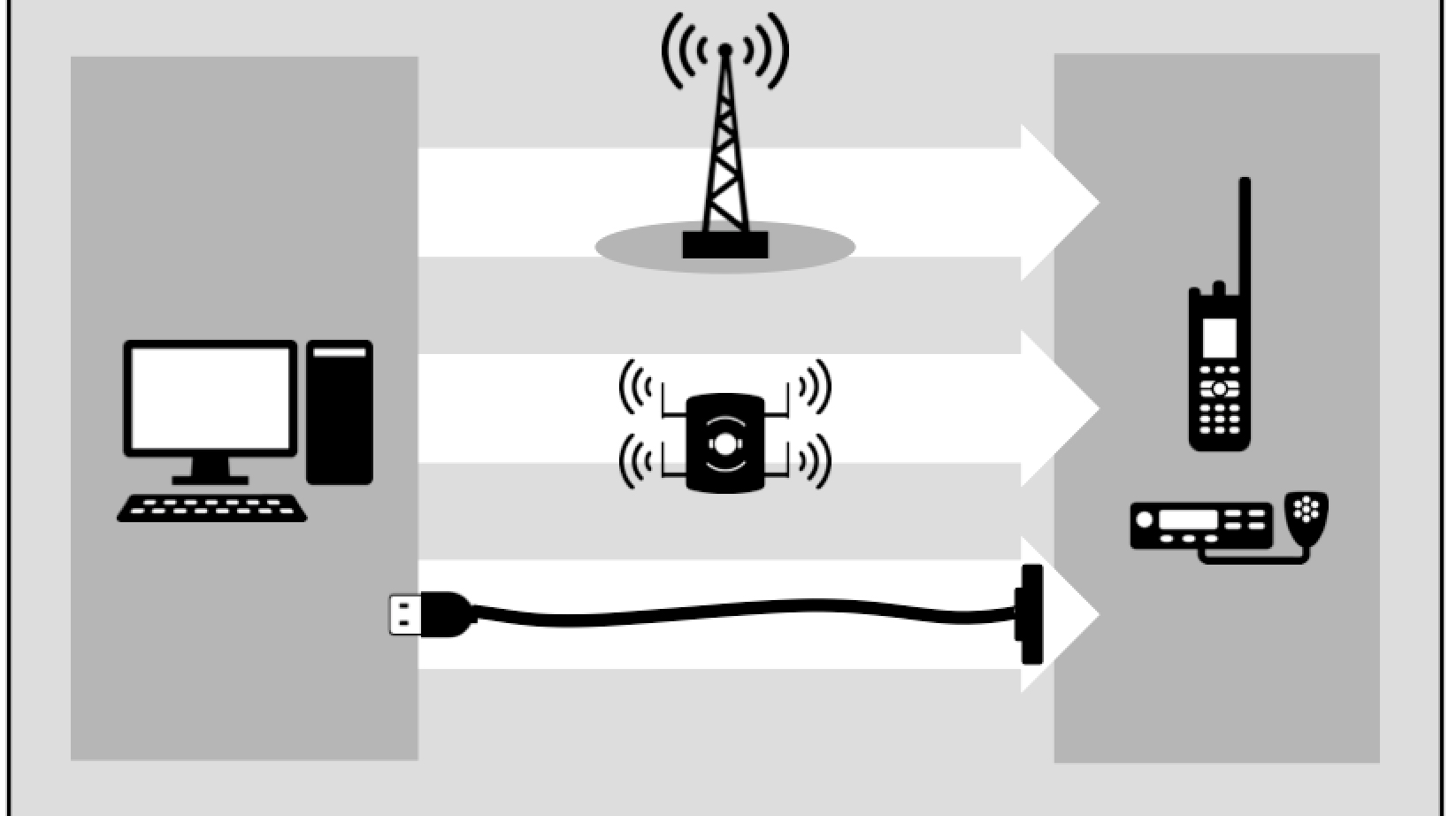
New threat actors are constantly emerging and posing risks to public safety agencies. However, you can take steps to protect your networks and mission-critical systems, such as enforcing multi-factor authentication, keeping your systems up-to-date with patching, establishing secondary forms of communication and more. You can also prepare your employees for an attack by conducting cyber exercises and joining a threat intelligence-sharing organization like the PSTA.
About the Public Safety Threat Alliance
The PSTA is an information sharing and analysis organization (ISAO) established by Motorola Solutions and is recognized by the Cybersecurity and Infrastructure Security Agency (CISA). The PSTA regularly publishes research, such as the 2022 Cyber Threats to Public Safety report, that is shared with members. It also hosts regular webinars featuring our cybersecurity analysts and other experts. The PSTA provides threat intelligence for member public sector organizations at no cost.
Join the PSTA today to get your copy of the 2023 Emerging Threat Actors report.