Cyber attacks on public safety answering points (PSAPs) increased almost 40 percent from August 2020 to the beginning of 2021, according to a recent Motorola Solutions report. With high potential payouts and a low chance of apprehension — much less prosecution — attackers show no signs of slowing down. Many PSAPs simply don’t have the resources they need, though, to effectively strengthen their defenses.
To help agencies get a better understanding of the fundamentals of cybersecurity for emergency communications, we recently published When Lives Are on the Line: Protecting PSAPs From Cyber Attacks. This in-depth guide covers questions such as:
- What are the best security and organizational practices to implement?
- How do you ensure a high level of security with whatever budget and resources you have?
- What’s the best way to get started?
The guide examines the most critical threats to dispatch centers and Emergency Communications Centers (ECCs) that handle 9-1-1 calls. It also offers recommendations for what to consider when exploring and evaluating solutions to keep them secure. Here are some of the highlights.
The Most Pressing Threats to 9-1-1 and Dispatch
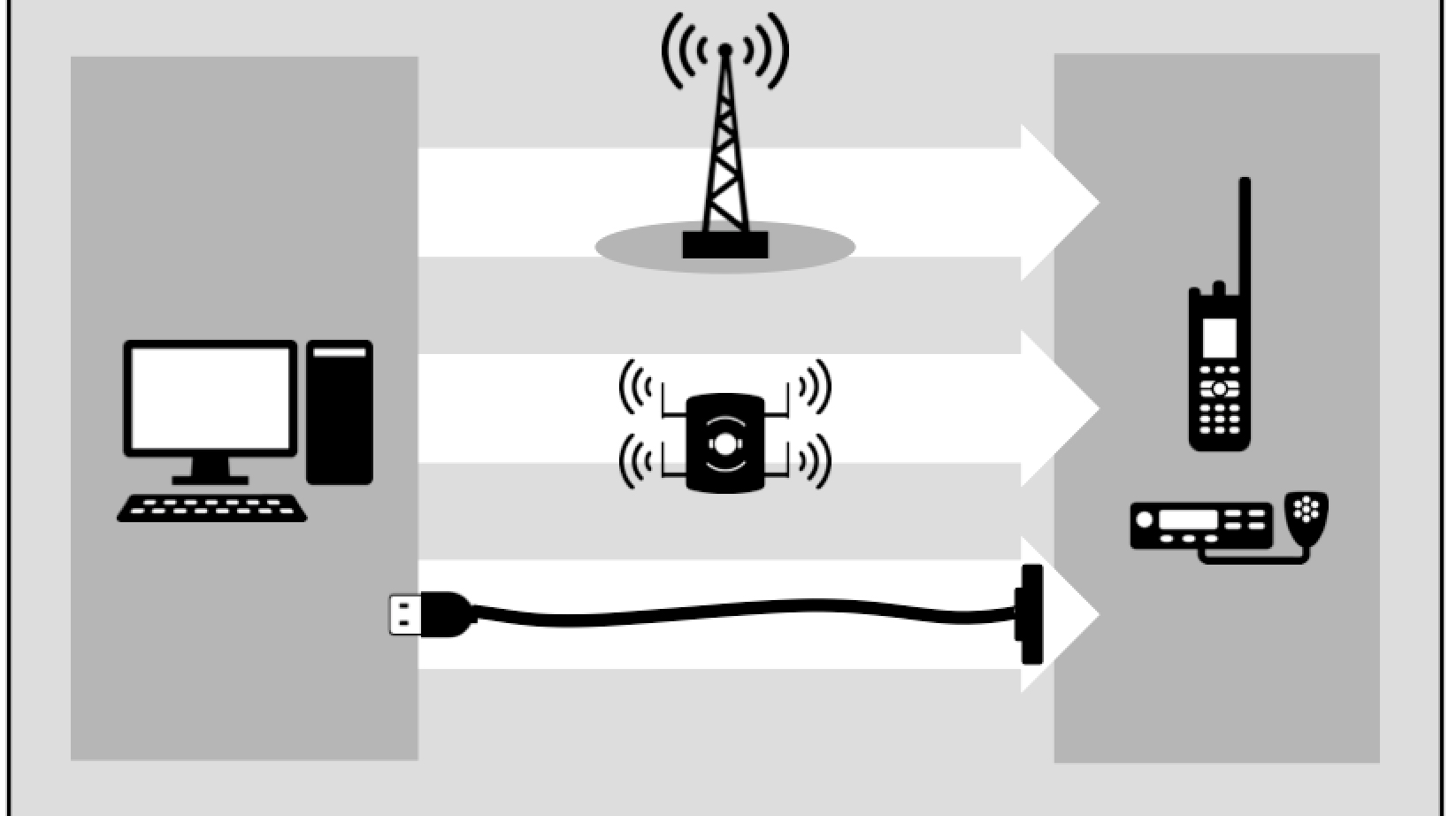
The two main threats to PSAPs are ransomware and Telephony Denial of Service Attacks (TDoS). Ransomware is the most common cyber threat, impacting computer-aided dispatch (CAD) systems in two ways, as we noted in the recently-published 2021 Threats to Public Safety: Criminal Operations Focus. The first is via indirect attacks on municipal and public safety networks, which often work as the backbone networks for CAD systems. The second directly compromises public safety networks themselves.
Distributed Denial of Service (DDoS) attacks are a well-known type of cyberattack that tries to make a website or network resource unavailable by flooding it with malicious traffic so that it is unable to operate. For PSAPs, that typically takes the form of Telephony Denial-of-Service (TDoS) attacks, often initiated through botnets and Voice over Internet Protocol (VoIP) services. They continue to represent a significant threat to emergency communications availability.
7 Best Practices for Protecting PSAPs
With limited time and budgets, it’s important to prioritize investments that protect the most critical parts of your mission. Our new guide goes into more detail on seven foundational best practices to get you started:
- Know Your Risks. Regular risk assessments can give you a better understanding of your vulnerabilities to help you make more informed decisions. By understanding where your weak points are, you can prepare an effective response plan to protect your mission-critical systems in the event of a security incident.
- Take Ownership of Securing Your Organization’s Technology. To ensure everyone is communicating about security issues, it’s important to proactively designate one person within your PSAP to own the operational side of your system, whether that’s a Chief Information Security Officer (CISO) in larger agencies, or an IT director in smaller organizations.
- Empower Yourself with Knowledge about Security Standards. The National Institute of Standards and Technology (NIST) established a common framework under Special Publications (SP) 800-53-revision 5 that provides a solid foundation for anyone establishing or revamping their cybersecurity program.
- Patch, Patch, Patch. Regular patching to apply security updates is one of the most efficient and cost-effective actions you can take to lower your exposure to cybersecurity threats. Before applying patches to mission-critical systems, be sure they’ve been tested in a lab environment to identify any impacts to other interconnected systems and address them before going live.
- Upgrade Hardware. Many manufacturers no longer support older systems and devices, so they rarely, if ever, push out security patches for them, regardless of existing,well-known vulnerabilities. This makes it essential to budget and plan for regular hardware updates.
- Monitor Security Alerts from CAD Endpoints 24/7. By deploying endpoint detection and response (EDR) agents to monitor for attacks on CAD workstations and servers, security analysts can see potential threats in real time and remediate them quickly.
- Understand Attacker Motivations via Threat Intelligence. Knowing what motivates different threat actors can help you determine what tactics they might use against your agency. Understanding and applying countermeasures from shared public safety threat intelligence can enable you to respond faster to attacks.
Help Is Available
It’s no longer a matter of if, but when and how your PSAP will become a target for cyber attackers. Yet, as our guide explains, help is available. Motorola Solutions, a Managed Detection and Response (MDR) service provider, offers a complete managed security solution to surface risks, identify imminent threats and provide a quick response to mitigate cybersecurity attacks around the clock. Ask the right questions and confidently take the first steps on the road to finding the right MDR service provider for your PSAP. When lives are the line, your community deserves nothing less.
Download When Lives Are on the Line: Protecting PSAPs From Cyber Attacks now to read the full guide (no registration required).