According to Motorola Solutions’ most recent review of the public safety threat landscape, attacks on PSAPs have greatly increased in the past two years. From the second half of 2020 to the beginning of 2021, there was a 38 percent jump in reported cyber attacks against public safety agencies. Ransomware made up almost 50 percent of these attacks, with financial extortion or stolen data as the main objective. These new threats present a variety of operational challenges and potential impacts on emergency communications.
To give agencies an in-depth look at how Motorola Solutions can help them better defend their organizations, we recently presented the webinar, “Security from the Start: Protecting PSAPs From Cyber Threats.”
Presenters shared insights on the top cyber threats impacting PSAPs and how agencies can level the playing field, centered around a holistic approach to cybersecurity. Here are some of the highlights.
Detecting Threats Faster
John Hawley, Chief Product Officer for Motorola Solutions Cybersecurity Services, discussed the rationale behind our ActiveEye Managed Detection and Response (MDR) platform and how it keeps agencies safe from potential threat actors.
“The adversary is moving very quickly,” Hawley noted. “They have advanced capabilities and the battle today is really hands on keyboards. Meaning, can you implement capabilities that are as strong as the adversary?”
Hawley explained that MDR provides two primary capabilities that help organizations defend against cyber adversaries. First, the ActiveEye platform pulls security data from monitored environments and has functions that allow it to automatically initiate actions against many known threats. Secondly, there’s a 24/7 team of experts who are very familiar with the ActiveEye platform. These experts know what needs to be done in any given situation and quickly respond to threats that aren’t automatically remediated by the platform.
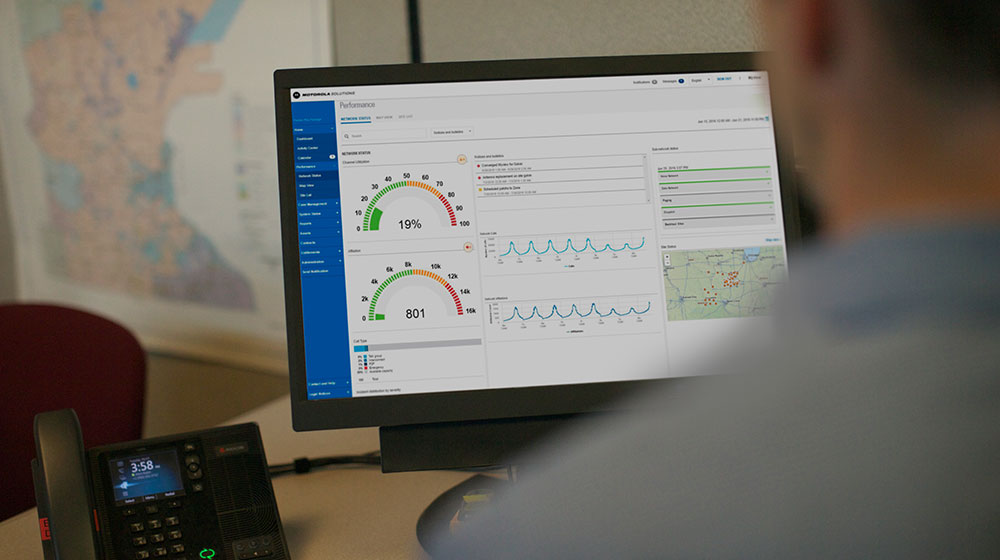
One differentiating feature of ActiveEye is its co-managed portal. It allows organizations to see exactly what our Security Operations Center (SOC) analysts are seeing.
“What we found when we looked at the market early on was a lot of dissatisfaction with managed security providers because they were essentially a black box,” Hawley said. “There was no visibility into what was going on within the environment. In response, we created a customer-facing interface within ActiveEye that simplifies the view of all threat activity. This gives our customers the ability to see everything the security operations team is doing on their behalf.”
ActiveEye customers have access to every alert, key metrics around response times as well as granular details of investigations, communications and mitigation actions. “It’s really a very transparent pane of glass in terms of what the team is doing on their behalf,” Hawley explained.
Exploring the Risks Your Organization Faces
Ryan Clancy, a senior consultant for the Motorola Solutions Advisory Services team, leads security assessments for clients globally. He’s seen firsthand the benefits agencies receive from cyber risk assessments.
“Today, when we’re integrating systems together, a risk that’s experienced by one system is now borne by all systems,” he said. “That can become a problem if people onboard systems into their environment that have vulnerabilities or are prone to becoming out of date.”
He continued, “The thing that I love about risk assessments is that they’re very holistic. The way that we start with a risk assessment is to begin looking at the top down, starting with understanding what an organization does. Then, we get progressively more technical as we move forward with the assessment.”
Clancy explained that risk assessments provide two primary values. First, they enable a CIO, a CSO or an IT Director to see parts of the organization they might not normally see. “It gives them an excuse to be able to walk around their organization, to find out more about the risks in different parts of their organization.”
Second, risk assessments provide a clear roadmap of organizational risk and a prioritized list of recommendations for resolving them, understanding that money, time and people are all scarce resources. “Having a prioritized list allows an organization to only focus on fixing the most important of those at a time, as resources allow,” Clancy said.
Sharing Public Safety Threat Intelligence
The final panelist, Jay Kaine, is the Director of the new Public Safety Threat Alliance (PSTA). The PSTA is a cyber threat Information Sharing and Analysis Organization (ISAO) that Motorola Solutions recently established that’s recognized by the Cybersecurity and Infrastructure Security Agency (CISA).
Explaining the nature of the PSTA, Kaine shared that “Our organization, as we continue to build it out, is dedicated to the sharing of information and intelligence across public safety. There was a demand from federal, state and local partners for an initiative like this since there wasn’t a threat intelligence sharing organization focused on public safety before.”
Summary
As attacks against PSAPs and adjacent systems increase, they present a variety of operational challenges and potential impacts. Today, protecting PSAP systems from cyber attacks requires a holistic approach to cybersecurity. To learn more about how Motorola Solutions helps secure mission-critical PSAPs, we invite you to watch the on-demand webinar, “Security from the Start: Protecting PSAPs From Cyber Threats.”